Reporting a data breach: How companies react correctly
Ein Datenverlust oder Datendiebstahl (auch „Data Breach“ genannt) kann für Unternehmen und betroffene Personen schwerwiegende Folgen haben – von finanziellen Einbußen über rechtliche Konsequenzen bis hin zu empfindlichen Reputationsschäden. Die Ursachen für einen solchen Datenschutzvorfall sind vielfältig: Cyberangriffe durch Hackergruppen, ein Fehlversand von E-Mails oder Dokumenten, der Verlust unverschlüsselter Datenträger oder auch technische Fehlkonfigurationen, die zu einem Verlust oder Abfluss von Daten führen können. Wie müssen Unternehmen bei einem Datenschutzvorfall oder einer Datenpanne vorgehen und wann müssen Sie nach der DSGVO Vorfälle melden?
If a data protection incident becomes known in the company, a quick, clear and structured approach is crucial in order to comply with the statutory reporting and notification obligations to supervisory authorities and data subjects (and, if applicable, to clients).
What is a data breach?
According to Art. 4 No. 12 GDPR, a data protection incident (data breach) is defined as a breach of security leading to the destruction, loss, alteration, unauthorized disclosure of, or access to, personal data transmitted, stored or otherwise processed.
A data protection incident occurs whenever an unauthorized act - i.e. unlawful processing - impairs (or may impair) the confidentiality, availability or integrity of personal data.
Examples of data breaches:
- Cyberattack: Hacker attacks or ransomware attacks that encrypt or steal data
- Misdirected emails: Personal or confidential data is inadvertently sent to the wrong recipient
- Loss of data carriers: Unencrypted USB sticks, laptops or external hard drives are lost
- Technical errors: Misconfigurations or software errors lead to unauthorized access to data.
When does a data breach have to be reported?
In the event of a data breach, there is an obligation to notify the competent data protection authority if the incident is likely to result in a risk to the rights and freedoms of data subjects (see Art. 33 GDPR). The deadline for this notification is 72 hours after the incident becomes known.
If there is even a high risk to the rights and freedoms of the data subjects, they must be notified without undue delay (see Art. 34 GDPR). Notification can only be omitted if, for example, the data concerned is protected by suitable technical and organizational measures (e.g. encryption), subsequent measures have completely eliminated the high risk or, exceptionally, a disproportionate effort is involved and a public announcement is made instead (cf. Art. 34 para. 3 GDPR).
Companies are therefore under considerable time and action pressure to quickly analyze the incident, draw the right conclusions and initiate appropriate measures.
Examples of a “high risk”:
🚨 Identity theft or fraud
🚨 Financial loss for affected persons
🚨 Discrimination through published data
🚨 Health data or other sensitive information have been disclosed
Evaluation of “risk” and “high risk”
As soon as a data protection incident becomes known, the controller must immediately take measures to contain it and assess the risk for the data subjects. This assessment is used to decide whether it is necessary to notify the supervisory authority and inform the data subjects. A risk exists in particular if there is a threat of physical, material or immaterial damage (see recital 75 GDPR).
The distinction between “risk” and “high risk” is often complex in practice. Guidance is provided by the opinions of the supervisory authorities and the European Data Protection Board (EDPB) Guidelines 9/2022 on the notification of personal data breaches under the GDPR. In particular, discrimination, identity theft or fraud, financial loss, damage to reputation and the disclosure of special categories of personal data (e.g. health data, ethnic origin or political opinion) are cited as examples of a high risk.
The risk assessment includes in particular
- the type of breach (e.g. breach of confidentiality or availability),
- the sensitivity, scope and identifiability of the data concerned,
- the severity of the possible consequences (e.g. identity theft, damage to reputation),
- Special characteristics of the affected persons (e.g. children)
- and the controller (e.g. medical facility) must be taken into account.
The risk is determined by the interplay between the severity of the impact and the probability of occurrence. For example, the EDPB states that a ransomware attack on a hospital generally entails both a notification obligation to the supervisory authority and a obligation to notify the persons affected, whereas an incorrectly sent email does not always have to be reported.
What content must the notification contain?
When notifying the supervisory authority, the controller must provide the following information (see Art. 33 (3) GDPR):
- Description of the breach: Type of data breach, specifying the categories of data affected, the approximate number of data subjects and data records affected.
- Contact information: Name and contact details of the data protection officer or a responsible contact point for queries.
- Impact assessment: Description of the likely consequences of the data breach for the data subjects.
- Measures taken: Description of the measures taken or planned to remedy the data breach and to limit the damage.
What documentation obligations exist?
Regardless of whether a reporting obligation exists, every breach must be recorded in internal documentation (see Art. 33 para. 5 GDPR and Art. 5 para. 2 GDPR on the principle of accountability). The supervisory authority can request this documentation at any time. The following points should therefore be recorded internally:
- Nature of the data breach, including cause and data affected
- Potential impact and consequences for the persons concerned
- Remedial measures taken to limit damage
- Explanation if no notification is made to the authority
How are data breaches at processors to be handled?
If a data protection incident occurs at a processor and personal data of the client (as controller) is affected, the processor must inform the controller without undue delay (see Art. 33 para. 2 GDPR). Often, even shorter deadlines (e.g. 24 hours) are provided for in the data processing agreement (DPA). It does not matter whether there is a risk to the data subjects; all relevant incidents must be reported. As the processor has a duty to assist the controller, the notification should cover the key points from Art. 33 para. 3 GDPR (description of the breach, contact information, impact assessment, measures).
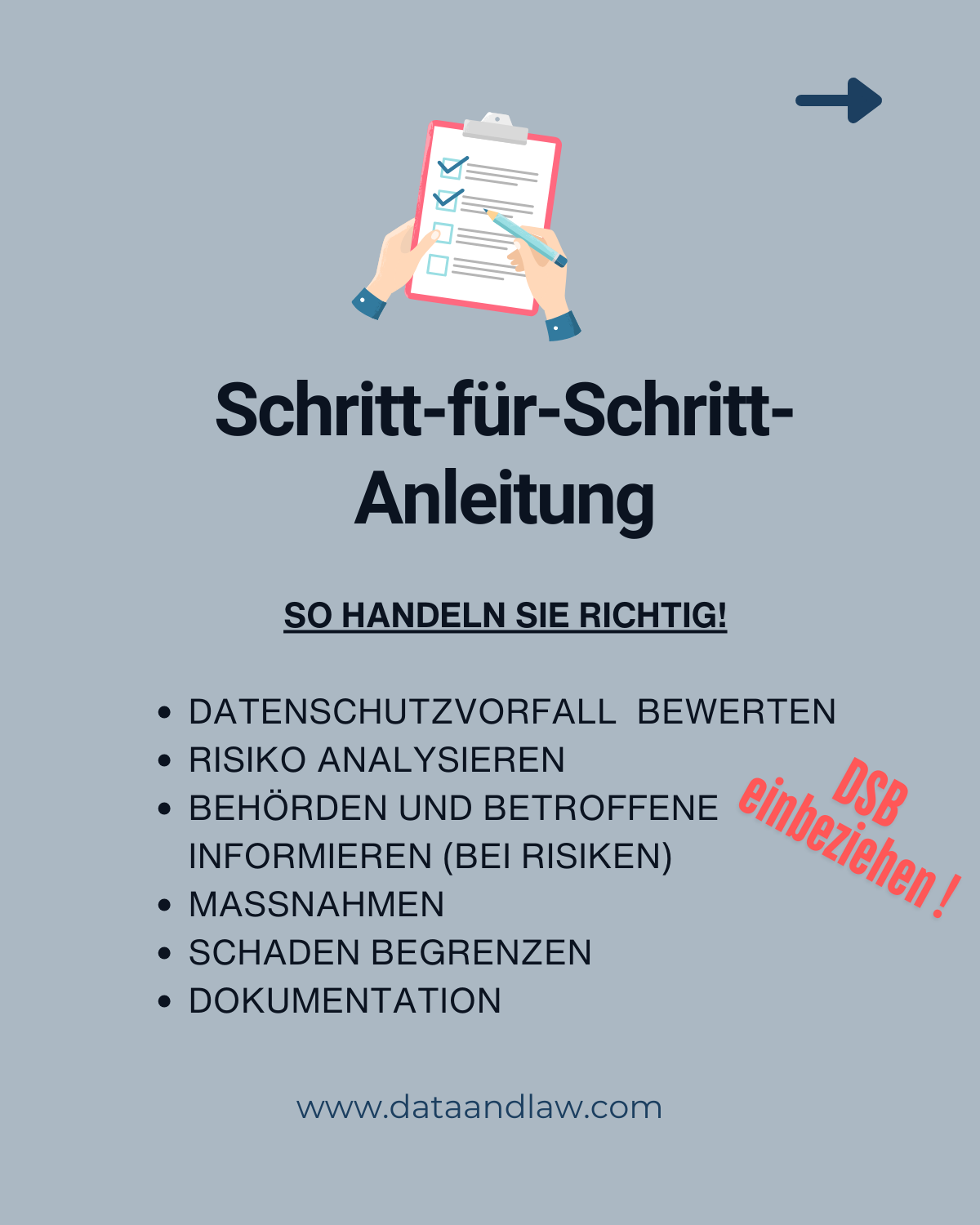
Step-by-step: managing data breaches correctly
Companies should implement a documented process with clearly defined roles and responsibilities. This process must cover the following steps and reporting lines in particular:
| 1. Identification & initial assessment | Report breach or suspicions → Inform IT & data protection officer (DPO) |
| 2. containment & investigation | IT secures systems, DPO collects information |
| 3. risk assessment & decision | DPO assesses risk, proposal for decision on notification to authority and affected parties, involvement of legal department and management |
| 4. Notification & communication | Adhere to deadlines: 72h for authorities, without delay for affected individuals; involve corporate communications |
| 5. follow-up & prevention | Analysis, documentation, adaptation of security measures, training of employees |
Summary
Data breaches can have significant consequences for companies and data subjects. A clearly defined process with clear responsibilities is therefore essential. Quick identification of an incident and immediate measures to contain it, as well as a thorough risk assessment and comprehensive documentation, are crucial. Regular employee training helps to prevent data breaches from occurring in the first place. Careful follow-up allows effective preventive measures to be derived and the risk of future incidents to be significantly reduced.